Dirty Frag is a vulnerability in Linux that allows an attacker to gain higher access or permissions than they are normally allowed on the system
This vulnerability was disclosed earlier than planned due to an embargo break, which means information about the vulnerability was released publicly before the agreed-upon disclosure date.
It’s a part of Linux kernel page cache exploits — following Dirty Pipe (2022) and Copy Fail (earlier this year).
What are Linux kernel page cache exploits?
The page cache in Linux is a system memory area where frequently accessed file data is temporarily stored.
It speeds up file operations because reading from memory is faster than reading from disk.
However, if an attacker can manipulate the page cache incorrectly, they can sometimes modify memory in ways they shouldn’t, bypassing normal permissions.
So, the dirty Frag uses two Linux kernel bugs (xfrm-ESP Page-Cache Write and RxRPC Page-Cache Write) together and tricks the kernel’s page cache to gain root access.
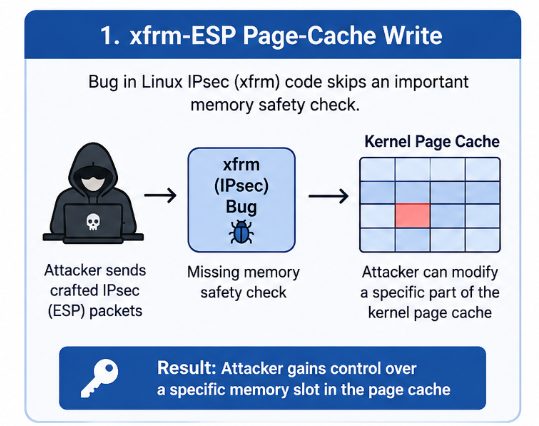
xfrm-ESP Page-Cache Write —The bug exists in Linux’s IPsec networking code, where it skips an important memory safety check.
This bug lets an attacker change a specific part of the kernel’s memory cache, giving them control over that memory, which is a key part of how the Dirty Frag exploit works.
RxRPC Page-Cache Write —
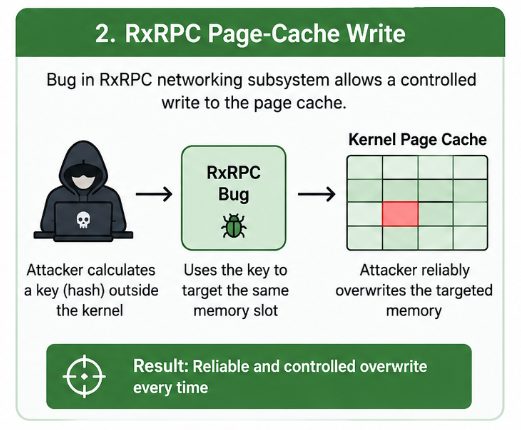
Another part of Dirty Frag exploits a bug in the RxRPC networking subsystem.
The attacker calculates a key outside the kernel, then uses it to safely overwrite memory, making the exploit work every time.
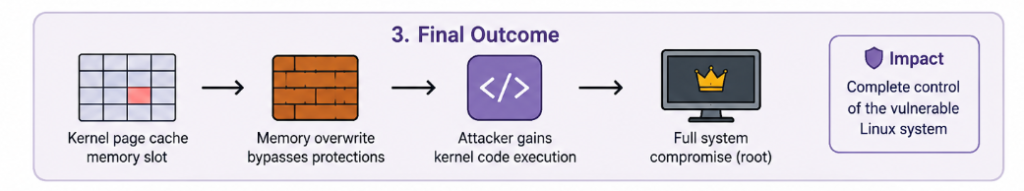
The (xfrm-ESP Page-Cache Write) vulnerability affects all recent Linux versions released since 2017. Any unprivileged local user can exploit it to gain full root (administrative) control.
The xfrm-ESP Page-Cache Write vulnerability has existed since 2017, while the RxRPC Page-Cache Write vulnerability appeared in June 2023
To exploit the Dirty Frag vulnerability, an attacker needs some level of initial access to the system. This could include:
- compromised website
- vulnerable application
- stolen SSH credentials.. etc
Once an attacker has this initial foothold, they can attempt to escalate privileges to root using Dirty Frag.
The following are the kernel versions where researchers successfully tested the Dirty Frag exploit:
- Ubuntu 24.04.4 → kernel 6.17.0-23-generic
- RHEL 10.1 → kernel 6.12.0-124.49.1.el10_1.x86_64
- openSUSE Tumbleweed → kernel 7.0.2-1-default
- CentOS Stream 10 → kernel 6.12.0-224.el10.x86_64
- AlmaLinux 10 → kernel 6.12.0-124.52.3.el10_1.x86_64
- Fedora 44 → kernel 6.19.14-300.fc44.x86_64
This means that if your server is running one of these kernels, it is likely vulnerable.
Temporary workaround until the official patch is released :
Since no official patch was available when Dirty Frag was disclosed, a temporary workaround can help reduce risk.
This involves disabling the vulnerable kernel modules (esp4, esp6, and rxrpc) and clearing the page cache to prevent potential exploits.
This may affect VPN or IPsec services. The permanent fix is to update our systems with the patched kernel once your Linux distribution releases it
You can use the following command to disable the vulnerable kernel modules and clear the page cache:
sh -c “printf ‘install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n’ > /etc/modprobe.d/dirtyfrag.conf; rmmod esp4 esp6 rxrpc 2>/dev/null; echo 3 > /proc/sys/vm/drop_caches; true”
However, this mitigation comes with a drawback: it disables the esp4, esp6, and rxrpc kernel modules by preventing them from loading
This will break IPsec and RxRPC, which is chiefly used by the AFS distributed file system.
For most desktop systems and general-purpose servers, this has little to no practical impact.
However, organisations that rely on IPsec VPN tunnels using ESP mode should carefully evaluate the tradeoffs before applying this mitigation.
So if this is acceptable, we can mitigate this vulnerability.
Dirty Frag Mitigation on CloudLinux :
In terms of CloudLinux, the affected versions are :
CL7h, CL8 → CloudLinux kernel
CL9, CL10 → AlmaLinux kernel used by CloudLinux
We can also apply the temporary workaround mentioned above until a patched kernel is applied, but as mentioned before , applying this workaround may affect VPN or IPsec services.
For a permanent fix, you have to update to the patched kernel once it’s available in your CloudLinux stream.
Amazon has also acknowledged that the Linux kernel vulnerabilities related to Dirty Frag may affect systems with certain kernel modules loaded, such as esp4, esp6, ipcomp4, ipcomp6, or rxrpc.
Amazon’s suggested mitigations include:
- Checking which modules are loaded
(lsmod | grep -E “esp4|esp6|ipcomp4|ipcomp6|rxrpc”).
2. Disabling modules if they are not needed.
echo ‘install esp4 /bin/false’ >> /etc/modprobe.d/cve-copyfail2.conf
echo ‘install esp6 /bin/false’ >> /etc/modprobe.d/cve-copyfail2.conf
echo ‘install ipcomp4 /bin/false’ >> /etc/modprobe.d/cve-copyfail2.conf
echo ‘install ipcomp6 /bin/false’ >> /etc/modprobe.d/cve-copyfail2.conf
echo ‘install rxrpc /bin/false’ >> /etc/modprobe.d/cve-copyfail2.conf
3. Restricting creation of user namespaces (sysctl -w user.max_user_namespaces=0).
Since an official patch is not yet available, the recommended approach for now is to apply the suggested workarounds to mitigate the vulnerability. At the same time, staying aware of potential risks and promptly applying patches as soon as they are released is essential for maintaining system security.
Dirty Frag: Universal Linux LPE highlights the importance of strong Linux security practices. While Linux remains one of the most secure operating systems available, no platform is immune to vulnerabilities. Local privilege escalation flaws can become extremely dangerous when systems remain unpatched or poorly configured.
Organisations should focus on:
- Rapid patch management
- Security monitoring
- Least privilege policies
- Linux hardening
- Continuous vulnerability assessments
By combining proactive defence strategies with modern monitoring tools, administrators can significantly reduce the risk posed by Linux privilege escalation attacks.