SSH (Secure Shell) is a network protocol that allows secure remote access to a Linux server. Normally, users authenticate using a password when connecting via SSH. However, passwordless authentication using SSH keys provides improved security and faster login access. This guide explains how to configure passwordless SSH login using PuTTY and PuTTYgen. What Is Passwordless SSH Login? Passwordless SSH authentication uses a public and private key pair instead of passwords: Once configured, you can log in securely without entering a password. Step 1: Download Required Tools Download the following utilities: …
General Topics
Google has launched its new free tool called ‘Web Designer’ for building interactive HTML5 web sites and advertisements.This tool can be downloaded for Mac and Windows. It is a great means by which the advertisers can create HTML5 pages and animations very easily for mobile as well as PC. The best part about this latest release is that one can directly edit the source code in the editor which is built into it. The designers can later view the preview of their sites in the browser. One can further improve …
Bandwidth throttling is a deliberate technique used to control the amount of data that can be transferred over a network within a specific time period. It is commonly applied by internet service providers, hosting environments, firewalls, and applications to manage network congestion, maintain stability, and ensure fair usage of resources. While throttling is often misunderstood as general website slowness, it is important to distinguish intentional bandwidth limits from performance bottlenecks caused by inefficient code or server overload. What Is Bandwidth Throttling? Bandwidth throttling refers to the intentional limitation of upload …
Network Monitoring witn Ntop
There are various types of network problems that occur in an organization,which results in inaccessible devices,performance degradation, etc.These can be classified as: Network Hardware failure : Includes faulty devices like switches,Ethernet cards,improper cabling etc. Network configuration problems : Includes issues related to improper configuration of protocols Malicious code : Includes issues as a result of the presence of worms/viruses on the network In order to troubleshoot network problems from scratch you need to start checking by hardware – ie,physically check network cabling,network cables crossovers over electric cables,quality of switches routers …
A completely frozen Linux system can be frustrating. The mouse cursor does not move. Keyboard shortcuts like Ctrl + Alt + F1 or Ctrl + Alt + Backspace do not respond. Even the Num Lock key may stop toggling. In such situations, most users force a hard reset. However, a hard reboot can lead to data corruption or filesystem damage. There is a safer way to reboot a locked Linux system using the Magic SysRq key. This method allows you to properly terminate processes, sync disks, and safely reboot the …
Choosing the right hosting control panel is an important decision for hosting providers, businesses, and system administrators. Among the many options available, cPanel and Plesk continue to dominate the web hosting industry. Both are mature, reliable platforms, but they are built with different use cases and operating environments in mind. Understanding Hosting Control Panels A hosting control panel is a web based interface that simplifies server and website management. It allows administrators and end users to manage domains, email accounts, databases, DNS records, backups, and security settings without working directly …
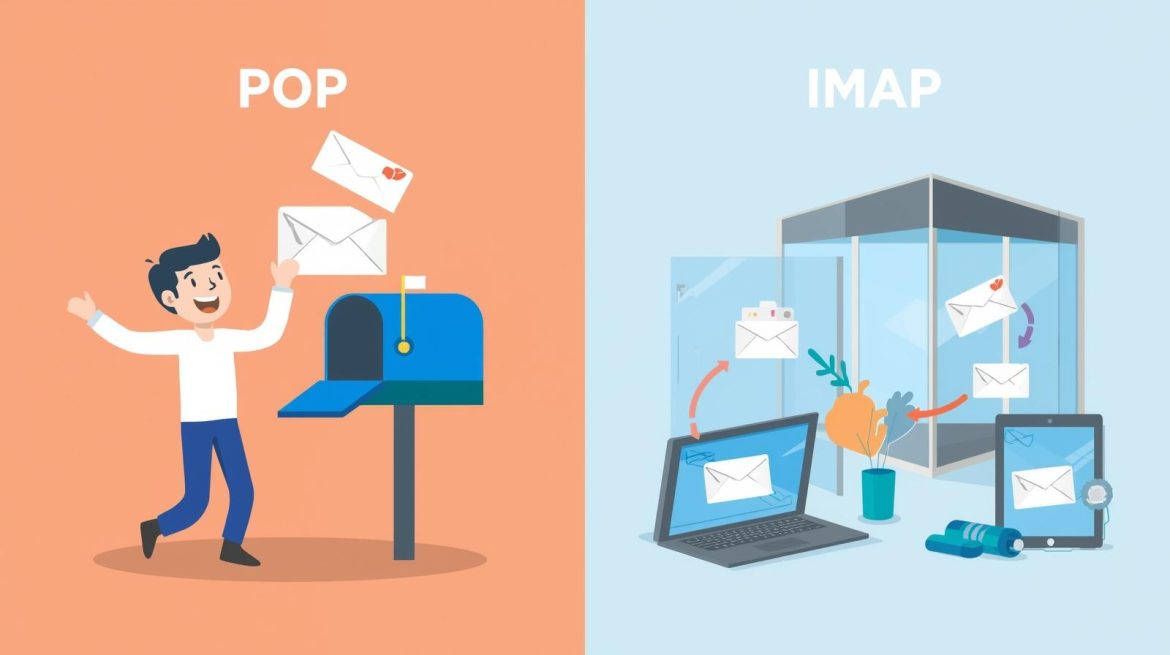
When configuring email, one of the most common decisions is choosing between POP and IMAP. Both are email retrieval protocols, but they work in very different ways. POP (Post Office Protocol) is an older protocol designed for offline email access. IMAP (Internet Message Access Protocol) is more modern and supports multi-device email access. Understanding the difference between POP and IMAP helps you choose the right setup for your business or personal email. What Is POP (Post Office Protocol)? POP was designed to download emails from the mail server to a …
As most of the mobile applications used today contain open source, 70% fail to comply with their respective licenses. From a recent survey conducted by OpenLogic, Inc., a leading provider of enterprise open source software support, announced that 71% of Android, iPhone, and iPad apps containing open source failed to comply with basic open source licensing requirements. They scanned 635 leading mobile applications in order to identify open source components and evaluate compliance with the relevant licenses. Applications that contain open source components are required to comply with the rules …
RAID stands for Redundant Array of Inexpensive Disks.The main purpose of raid is to increase logical capacity of storage devices used,improve read/write performance and ensure redundancy in case of a hard disk failure. Raid devices are marked by two letters and a number. Eg. md0,md1,md2. Raid is mostly used in large file servers where data accessibility is higher. Raid unit appears to be equivalent to a single large capacity disk drive. The remarkable benefit of disk array is that if any single disk in the RAID fails, the system and array still continues to function without …
Google Alerts were available from long back. Many of us have forgotten that it still exists. It provides email updates, so the latest appropriate Google results (web, news, blog, videos, discussions etc.) based on your search keywords. When you type query that you like to monitor, you will see a preview of the same. You can use Google Alerts to: Monitor a unfolding news story Keep updated on your competitor(s) or any industry Get the latest news about events Article Authored by Rosemary J Thomas Author, Rosemary J Thomas, is …