A sudden traffic spike on a Linux server can indicate a DDoS (Distributed Denial-of-Service) attack. Knowing how to detect DDoS traffic quickly helps prevent downtime, performance loss, and service disruption. During a DDoS attack, multiple IP addresses send massive amounts of traffic to your server, overwhelming system resources such as CPU, memory, or network bandwidth. This guide explains how to check if your server is under attack using built-in Linux commands.
What Is a DDoS Attack?
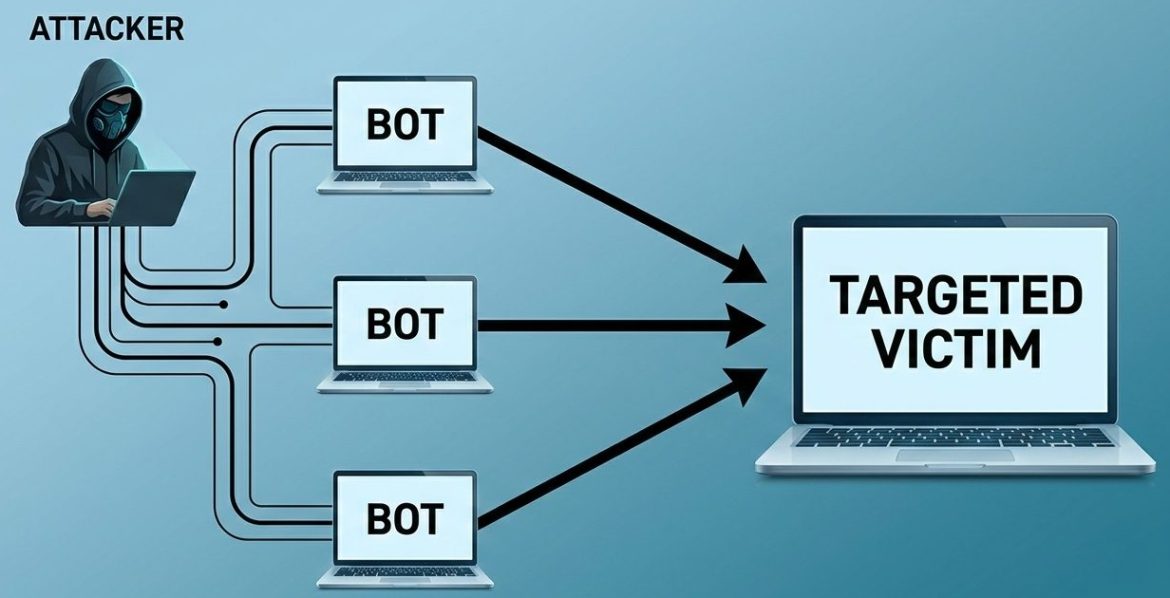
A Distributed Denial-of-Service attack occurs when attackers use multiple compromised systems to flood a target server with traffic.
The goal is to:
- Exhaust server resources
- Disrupt service availability
- Cause downtime
- Impact business operations
Modern DDoS attacks are often automated and highly distributed, making them harder to detect.
Quick Check (30-Second Test)
If you see:
- hundreds of connections from one IP
- many SYN_RECV states
- bandwidth maxed
- high load average
Your server may be under attack.
How to Check Active Connections by IP Address
One of the fastest ways to detect abnormal traffic is by identifying which IP addresses are making the most connections to your server.
Run the following command in your SSH terminal:
netstat -anp | grep 'tcp\|udp' | awk '{print $5}' | cut -d: -f1 | sort | uniq -c | sort -nNote: You may need
sudoor root privileges to view all connections.
Example Output
45 192.168.1.10
120 203.0.113.7This output shows:
- The number of connections
- The corresponding remote IP address
If one or a few IPs have an unusually high number of connections, your server may be under stress or attack.
Suspicious Connection Thresholds
| Server Type | Normal | Suspicious |
|---|---|---|
| Small VPS | <150 | >400 |
| App server | <800 | >2000 |
| High traffic | <5000 | >12000 |
What This Command Does (Step-by-Step)
This pipeline command:
- Lists all active TCP and UDP connections
- Extracts the remote IP address
- Counts how many times each IP appears
- Sorts IPs by connection count
It provides a quick snapshot of traffic concentration.
Alternative Command to Detect DDoS Connections
On newer distributions, netstat may not be installed by default.
You can use:
ss -antupThe ss command is faster and more efficient for viewing socket statistics.
Important: Why High Connections Alone Don’t Prove a DDoS
Modern DDoS attacks are more sophisticated.
Attackers may use:
- Thousands of distributed IP addresses
- Fewer connections per IP
- Rotating source IPs
- Layer 7 (application-level) attacks
In such cases, no single IP appears suspicious — but aggregate traffic overwhelms the server.
Always analyze:
- Traffic spikes in monitoring tools
- CPU and memory usage
- Network bandwidth consumption
- Access logs
Example suspicious log entry:
203.0.113.7 - - [10/Feb/2026:10:22:11] "GET /login HTTP/1.1" 429 -Inspecting Connection States and Ports
You can further analyze connection activity using:
View Established Connections
lsof | grep ESTABLISHEDShows currently active connections.
View Listening Services
lsof | grep LISTENDisplays services waiting for incoming connections.
Inspect a Specific Process
lsof -p PIDHelps identify which application is handling suspicious traffic.
This is useful for determining whether:
- A web server (Apache/Nginx) is targeted
- A database port is exposed
- A specific service is overloaded
Temporary Mitigation Options
If you identify a malicious IP, you can temporarily block it using firewall rules such as:
iptablesfirewall-cmd
However, manual IP blocking is not a long-term solution for large-scale DDoS attacks.
For production environments hosted on platforms like Amazon Web Services, built-in tools such as AWS Shield can provide automated mitigation.
Best Practices for DDoS Prevention
Beyond command-line checks, organizations should implement:
- Real-time monitoring systems
- Rate limiting
- Web Application Firewalls (WAF)
- CDN-based traffic filtering
- Load balancing
- Auto-scaling policies
Proactive planning reduces operational risk significantly.
Conclusion
Monitoring active connections is a quick and effective first step when investigating unusual traffic spikes. Commands like netstat, ss, and lsof provide immediate visibility into server activity.
However, modern DDoS attacks require a broader defensive strategy that includes proactive monitoring, structured escalation processes, and layered security controls.
Understanding traffic patterns early can help reduce downtime, protect infrastructure, and maintain service availability.
Frequently Asked Questions
How many connections from one IP is considered suspicious?
There is no fixed number. It depends on your server capacity and traffic patterns. Sudden spikes or unusual patterns are stronger indicators than raw numbers.
Can netstat detect all types of DDoS attacks?
No. It helps identify connection-based attacks, but application-layer attacks require log analysis and monitoring tools.
Should I block suspicious IPs immediately?
Temporary blocking may help, but improper firewall rules can block legitimate users. Always verify traffic behavior first.
How can I quickly check if my Linux server is under a DDoS attack?
You can run commands like ss -antup or netstat -an to inspect active connections. A sudden spike in connections, especially from multiple IPs or unusual states like SYN_RECV, may indicate suspicious traffic.
Need Expert Help?
If you suspect a DDoS attack or need help analyzing your server traffic, contact SupportPRO server administrators for immediate analysis and mitigation.