As organizations increasingly rely on cloud infrastructure, cybersecurity risks and regulatory requirements continue to grow. Businesses must protect sensitive data, maintain compliance standards, and ensure uninterrupted operations in rapidly evolving cloud environments. Basic infrastructure management is no longer enough. Managed cloud services provide continuous monitoring, advanced security controls, and compliance support that help organizations maintain secure, scalable, and compliant cloud environments. This guide explains how managed cloud services enhance cloud security, simplify compliance management, and improve overall business resilience. Why Businesses Choose Managed Cloud Services Managing modern cloud platforms internally …
Introduction Cloud computing has transformed how businesses scale and operate, but without proper control, AWS costs can quickly spiral. AWS cost optimization is not just about cutting expenses. It is about aligning cloud usage with actual business needs while maintaining performance and reliability. This guide explains how to manage AWS costs effectively, identify inefficiencies, and implement long-term strategies for sustainable AWS cost savings. Understand What is Driving Your AWS Costs To begin AWS cost optimization, you need full visibility into where your money is going. Key Areas to Analyze 1. …
Is Anonymous VPS Hosting Right for You? A Practical Guide to Secure, Scalable Enterprise VPS Hosting
Understanding Anonymous VPS Hosting in Modern Cloud Enterprise Anonymous VPS hosting allows businesses to operate virtual servers without linking infrastructure to personal or corporate identity. What makes it different 1. No or minimal KYC requirements 2. Cryptocurrency-based payments 3. Reduced digital footprint Why it matters for cloud enterprise 1. Supports privacy-first operations 2. Helps businesses run sensitive or experimental workloads 3. Aligns with evolving data protection concerns in cloud computing Anonymous VPS is not just about privacy. It plays a strategic role in modern cloud enterprise environments where control and …
Azure CLI Guide: Automating Cloud Computing for Business Efficiency
1. Why Automating Cloud Computing Matters for Businesses Automating cloud computing is no longer optional for growing organizations. As cloud environments expand, manual processes create bottlenecks, increase errors, and drive up operational costs. Key Benefits 1. Reduces repetitive manual tasks in cloud computing environments 2. Improves consistency across deployments 3. Enables faster decision-making with real-time insights Business Impact 1. IT teams spend less time on maintenance and more on innovation 2. Organizations gain better control over infrastructure lifecycle 2. How Azure CLI Improves Operational Efficiency Azure CLI simplifies cloud automation …
Explore server performance monitoring, provisioning automation, server migration, and maintenance strategies for small business infrastructure.
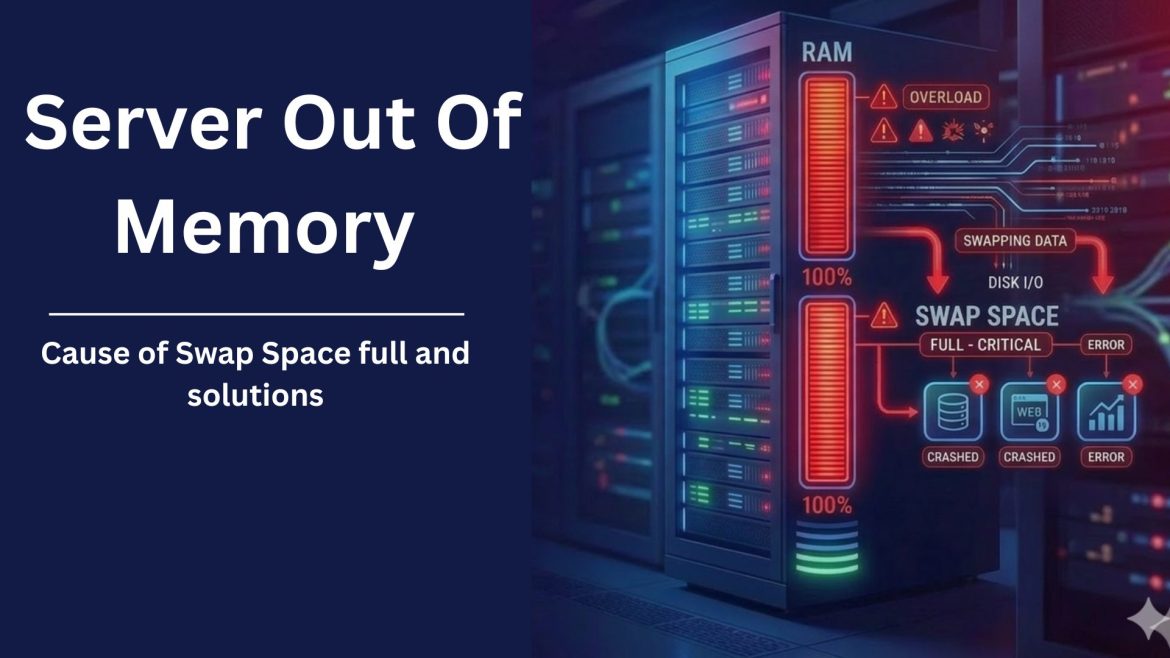
Server Out of Memory Errors: Why Swap Space Gets Full and How to Fix It
Server performance problems can be quite frustrating, especially when they happen again and again to the server. One common issue many VPS servers owners face is Server “Out of Memory” (OOM) errors. In this blog, we’ll explain what these errors exactly mean, why they happen, also in this memory issue, how swap space is involved, and what steps can be taken to reduce the problem. This blog is based on a real support case where a VPS server experienced repeated out of memory problems, MySQL crashes, and high or swap …
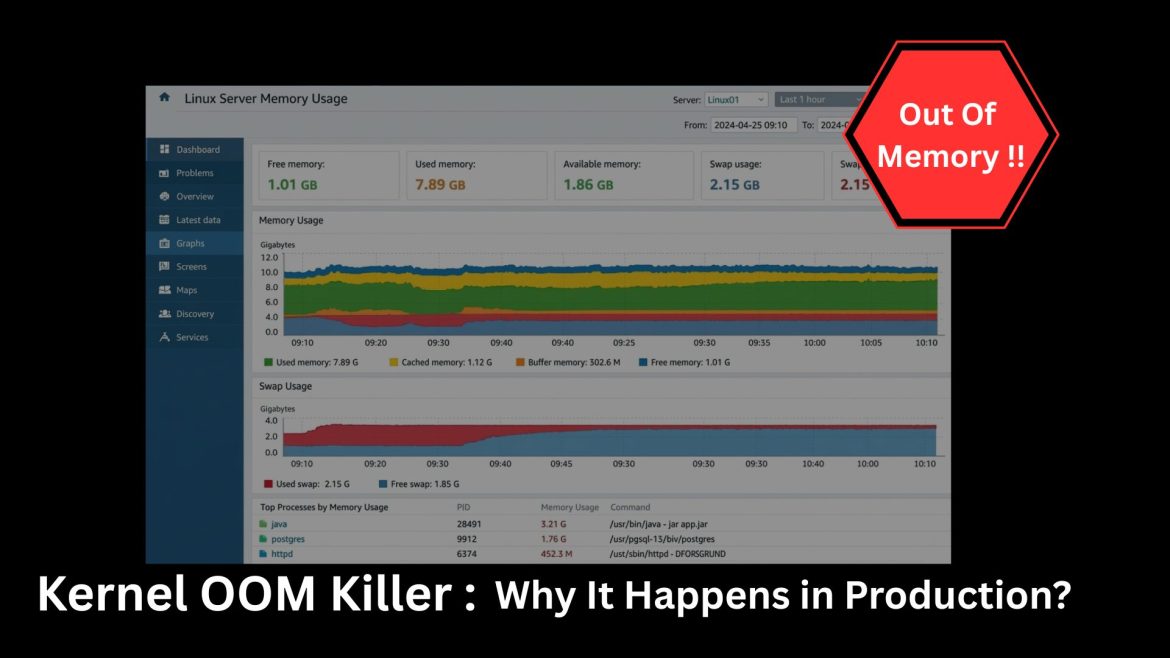
Modern applications run on complex stacks like containers, orchestration layers, cloud instances, microservices,all competing for memory. When memory pressure becomes critical, Linux activates a last-resort mechanism called the Kernal OOM Killer (Out-Of-Memory Killer). In production, this often shows up as a sudden crash with little warning, leaving engineers scrambling to understand what went wrong. Let’s break down what the Kernal OOM Killer really is, why it triggers, and how to prevent it. What Is the Kernal OOM Killer? The Linux kernel manages system memory. When available RAM and swap are …
Best Practices for Rotating Access Keys in Production Environments
In modern production environments, access keys are the lifeblood of secure communication between systems, services, and applications. They authenticate workloads, unlock APIs, and enable automation. Even though they play a critical role, access keys are frequently mishandled; kept the same for long periods, passed around between teams, or placed in locations where they shouldn’t be stored. When a key is compromised, the consequences can be catastrophic: data breaches, unauthorized access, service outages, and long‑term reputational damage. Rotating access keys is one of the simplest and most effective security practices organizations …
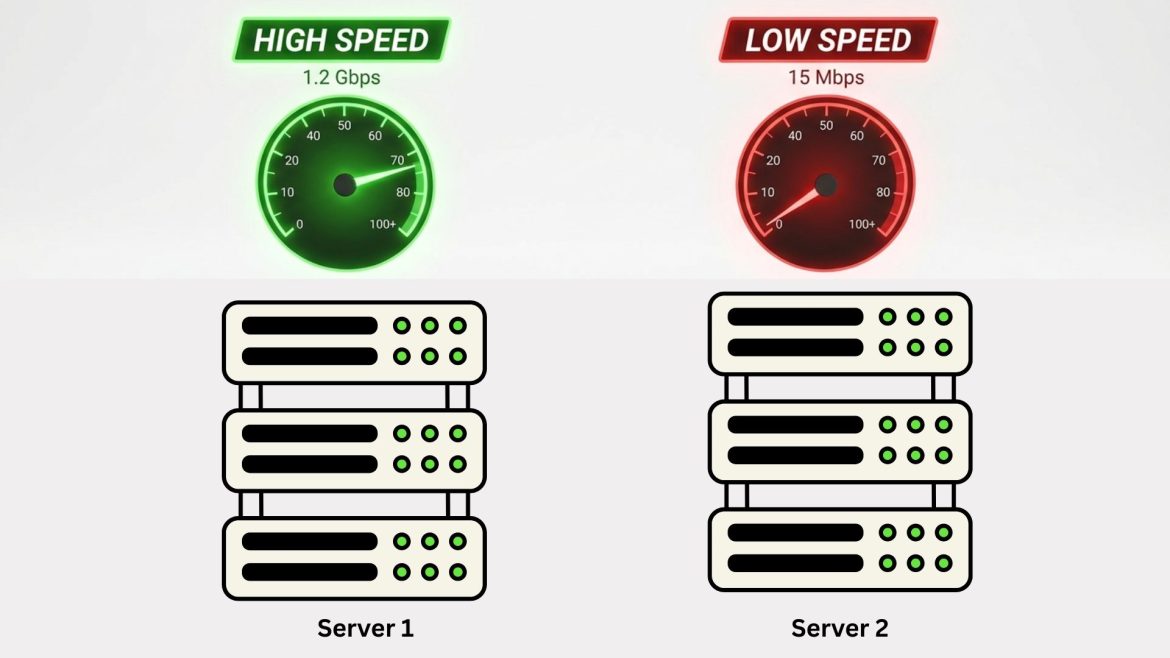
Why Cloud Instances Perform Differently Even with the Same Specs
If you have ever launched two cloud instances with identical specifications- same CPU, memory, storage, and operating system, you might expect them to perform exactly the same. In reality, that rarely happens. One instance might boot faster, handle traffic more smoothly, or complete workloads quicker than another, even though both look identical on paper. This inconsistency often surprises engineers, startups, and DevOps teams. After all, cloud providers advertise standardized virtual machines. So why does performance still vary? In this article, we’ll explore the real reasons cloud instances behave differently despite …
The Complete Guide to Email Archiving: Tools, Methods, and Best Practices
Managing business emails effectively has never been more critical. Emails are often the lifeblood of communication, legal evidence, and operational knowledge. Without a reliable system for archiving, businesses risk losing vital records, falling short on compliance, and creating knowledge silos that hinder collaboration. Email archiving is the systematic process of capturing, indexing, and securely storing all email communications in a centralized repository designed for long-term retention and easy retrieval. This practice ensures that business communications remain accessible, protected, and compliant with industry regulations. Why Email Archiving Matters Regulatory Compliance Many …