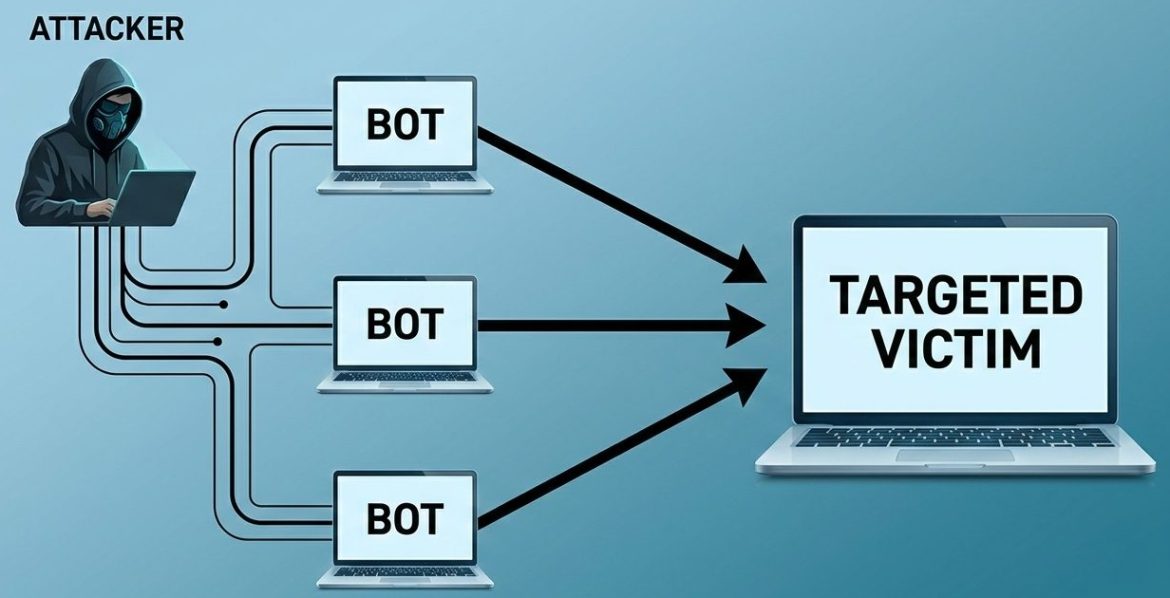
A sudden traffic spike on a Linux server can indicate a DDoS (Distributed Denial-of-Service) attack. Knowing how to detect DDoS traffic quickly helps prevent downtime, performance loss, and service disruption. During a DDoS attack, multiple IP addresses send massive amounts of traffic to your server, overwhelming system resources such as CPU, memory, or network bandwidth. This guide explains how to check if your server is under attack using built-in Linux commands. What Is a DDoS Attack? A Distributed Denial-of-Service attack occurs when attackers use multiple compromised systems to flood a …
How Remote IT Support Helps Businesses Resolve Issues Faster ?
The Hidden Cost of Slow IT Issue Resolution Every minute of IT downtime costs money. For mid-sized businesses, even one hour of downtime can cost thousands of dollars in lost productivity, missed transactions, and customer dissatisfaction. Traditional IT support models especially fully on-site teams often struggle with: As digital infrastructure becomes more complex, businesses need faster and more scalable support models. This is where remote IT support delivers measurable impact. But how exactly does it resolve issues faster? And more importantly, is it right for your organization? Let’s break it …
Common Server Support Gaps That Increase Operational Risk And How to Prevent Them
Modern businesses rely heavily on server infrastructure to maintain application availability, protect sensitive data, and support daily operations. Yet many organizations underestimate the operational risk created by gaps in server support. Even small inefficiencies: delayed responses, poor monitoring, weak escalation processes; can compound into extended downtime, compliance failures, and financial loss. Even a five-minute server outage can halt revenue, disrupt operations, and damage customer trust. According to industry reliability studies, downtime can cost enterprises thousands of dollars per minute depending on workload criticality. Understanding where server support commonly fails is …
For business, Email is the one of the most important communication tool. When your email working suddenly stop , then it can creation a confusion, delays and in some cases financial loss as well. Many peoples can immediatel think their email server is down or mailbox is broken. In Most of the cases, real issues lie in DNS settings and MX records . This blog, we will explain a common scenario where users stop receiving emails on their domain, why it happens, and how you can fix it step by …
Why “Cloud” Servers Still Go Down: Common Operational Mistakes
The word cloud often gives businesses a false sense of invincibility. Many assume that once systems move to AWS, Azure, or Google Cloud, outages become someone else’s problem. After all, cloud platforms promise high availability, redundancy, and scalability. Yet outages still happen and often in dramatic, business-disrupting ways. From e-commerce downtime to SaaS platform crashes, “the cloud” regularly reminds organizations that technology alone does not guarantee reliability. So why do cloud servers still go down? The answer usually isn’t the provider’s infrastructure. It’s operational mistakes made by the people designing, …
Why Poor Server Management Leads to Downtime and Security Risks ?
Servers sit at the core of business operations. Applications, customer data, internal systems, and digital services all depend on them. When server management is weak, the impact shows up quickly in the form of service outages, slow performance, and security incidents. For business leaders, poor server management is not an IT inconvenience. It is a direct risk to revenue, reputation, and operational continuity. What Happens When Server Management Is Poor ? How Poor Server Management Creates Downtime and Security Risks ? What Effective Server Management Looks Like ? Industry Trends …
How to Reduce IT Risks and Downtime with Remote Infrastructure Management ?
IT downtime directly affects revenue, productivity, and customer trust. As infrastructure environments grow more complex, traditional IT management approaches struggle to maintain stability and security. Remote Infrastructure Management, or RIM, helps businesses reduce IT risks and downtime by providing continuous monitoring, proactive maintenance, and faster incident response. What Causes IT Risks and Downtime ? A large proportion of infrastructure failures stem from operational gaps that could be detected or mitigated earlier, alongside unavoidable external or platform level events. 1. Hardware failures Aging or overloaded hardware often exhibits early warning indicators …
How to Troubleshoot AWS Load Balancer Issues: Timeouts, 5XX Errors, and Health Checks
It’s easy to forget about the load balancer when everything is going well on AWS. But you know how important it is as soon as you start to see wrong responses, weird typos, or health checks that don’t work. A misconfigured health check or a backend server that couldn’t keep up has stopped projects in their tracks. In this post, I’ll walk through AWS Load Balancer troubleshooting, covering common issues with AWS Elastic Load Balancers (ELB, ALB, and NLB), what typically causes them, and proven ways to fix them. 1. …
Many developers and DevOps engineers who work with Kubernetes eventually face the CrashLoopBackOff error. It can look scary at first. A container starts, crashes, and then keeps restarting again and again. This affects your application’s reliability and availability. If you have been using Kubernetes for some time, you have probably seen this error. The good news is that CrashLoopBackOff is common. It is also easy to understand once you know how Kubernetes handles container failures. Kubernetes assigns the status CrashLoopBackOff when a container inside a Pod keeps failing shortly after …
In modern production environments, Access key are the lifeblood of secure communication between systems, services, and applications. They authenticate workloads, unlock APIs, and enable automation. Even though they play a critical role, access keys are frequently mishandled—kept the same for long periods, passed around between teams, or placed in locations where they shouldn’t be stored. When a key is compromised, the consequences can be catastrophic: data breaches, unauthorized access, service outages, and long‑term reputational damage. 1. Importance of Access Key Rotation : From a technical point, access keys is similar …